The services below will increase your security and reduce your surveillance by governments and advertisers.
Here are my tips for maintaining on-line privacy:
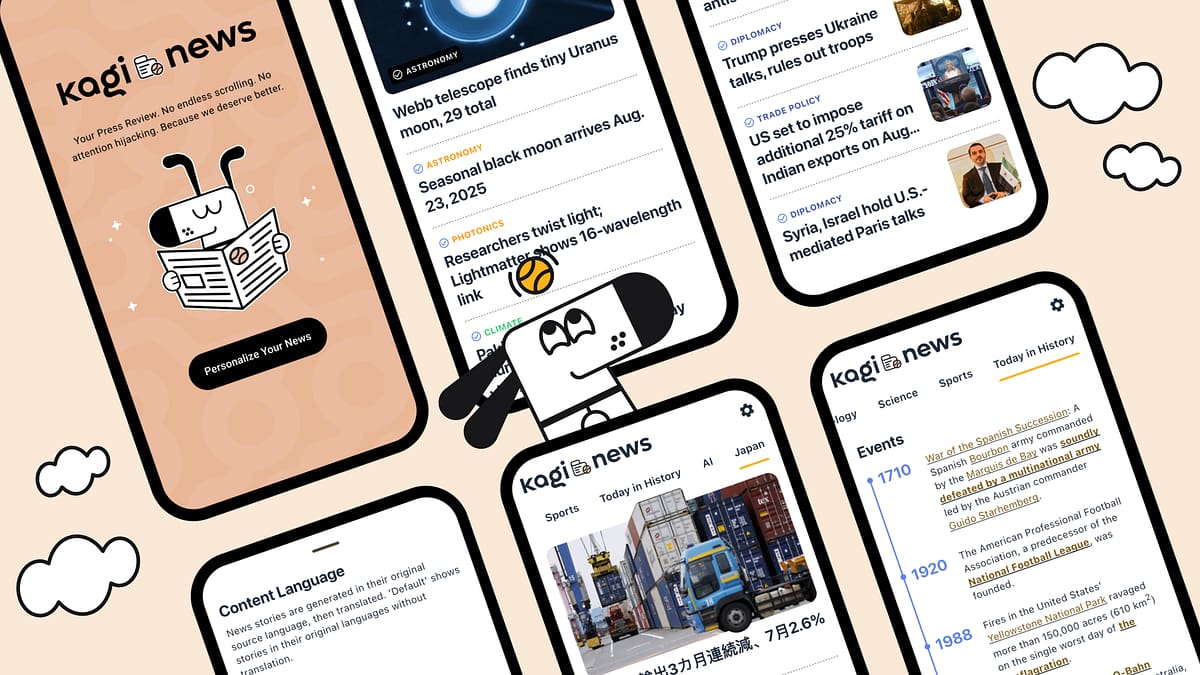
Use A Search Engine That Doesn’t Track You
Many popular search engines like Google and Bing save your search history. Typically, your searches are saved along with some information about your computer (e.g. your IP address, User Agent and often a unique identifier stored in a browser cookie), and if you are logged in, your name and email address as also recorded. With this information, your searches can be tied together. This means someone can see everything you’ve been searching, not just one isolated search. You can usually find out a lot about a person from their search history.
StartPage is a search engine that removes all identifying information from your query and submits it anonymously to Google.
DuckDuckGo is another good search engine with a focus on privacy. It does not record user information — see their privacy policy for the details.
See my article How To Make Your Searches Private, Ad-Free And Uncluttered for more details.
Move Away From Email Providers That Scan Your Email
FastMail is an independent email service that doesn’t scan your messages. Based in Australia, the service has been running for 15 years, and they have a good privacy policy regarding email storage. Here’s what they say:
- we use encrypted SMTP for sending your mail when the receiving server supports it
- we mandate encrypted access for webmail, IMAP and POP
- we use Perfect Forward Secrecy where possible for all encrypted connections
- we encrypt all email while at rest on our servers
- we encrypt communications between our data centers
FastMail‘s prices start at $10 per year.
If you need end-to-end email encryption, I recommend ProtonMail — a reliable encrypted email provider based in Switzerland.
See my article A List Of Email Providers That Don’t Track You for more information.
For a mail client, I recommend the open-source Thunderbird email client with JunQuila add-on to control spam.
Use A Privacy-Friendly Browser
Use a secure web browser like Firefox with privacy-mode turned on, and these add-ons installed: HTTPs Everywhere and uBlock Origin.
Tips on web browser privacy:
- Turn off third-party cookies — these are cookies that are sent to advertising firms. Turning off these cookies just means you’ll be tracked less — it won’t affect your browsing ability.
- I prefer to turn off cookies completely, and use the Cookie Whitelist add-on to only accept cookies from specific sites where I login
- You can install a extension like uBlock Origin (Firefox, Chrome) to block ads, thereby reducing the amount of information collected by advertisers
- The HTTPs Everywhere is an extension for the Firefox and Chrome browsers, made by the Electronic Frontiers Foundation. It encrypts your communications with many major websites, giving you a basic level of web browsing privacy.
- You can turn off Java and Flash in your browser (both can be a security risk — see an explanation here)
- You can install an extension like No Script (Firefox only), which stops web pages loading and running Javascript, Java and Flash. Using No Script can be tedious but it protects against attacks like Cross-Site Scripting (XSS) and Clickjacking (a trick that causes you to click and run a malicious program)
- If you want to browse anonymously, use the Tor Browser Bundle. It is a free application that is available for Windows, Macs and Linux. See my article on Tor for more details.
Keep Your Personal Information Private
Today, many companies want to collect your personal information in databases. Here are some tools to avoid this process:
- The Fake Name Generator is a free tool that instantly creates a set of fake credentials, for dealing with companies that request unnecessary personal information. It will create a completely fictitious identity that includes a fake name, telephone number, email address, street address and credit card number.
- SpamGourmet is a free service that allows you to create an unlimited number of disposal email addresses. See my article where I explain how to use this service.
- Safe Shepard is a free service that removes your name from various “people search” databases (e.g. PeekYou).
- The Account Killer websites gives your instruction about deleting yourself from sites like Facebook and Twitter. See also Permanently Deleting Accounts on Popular Websites.
You can read about other ways to opt-out here.
Use A Password Manager
Password managers allow you create strong, unique passwords for all your websites accounts. They will then automatically log you into websites, thus preventing key-logging (attempts to capture your keystrokes and hence your passwords).
An excellent password manager is Bitwarden.
Use A VPN To Avoid Snoopers
ExpressVPN is a virtual private network (VPN) service that is fast and reliable. It’s my top pick for a VPN (see more details here). Prices are $58 per year, or $9 per month.
See my article The Best VPNs for a list of all my recommended VPN providers.
You may wish to get a VPN-capable router. The router will provides a VPN connections to all your computers and mobile devices. You won’t have to install a VPN client on each device, all those connected devices count as one connection with your VPN provider.
FlashRouters sells routers with a VPN pre-installed. See my article The Best VPN Routers for more details.
Use Privacy-Friendly Forums
I recommend these apps for creating private forums and social networks: Discourse or BuddyPress.
Retroshare is a free, open source messaging system for encrypted “friend-to-friend” communication.
Here are some open source, federated apps for create forums: Buddycloud, Friendica, Movim or Pump.io
Diaspora* is a free open source social network. It’s a community-run distributed network so there’s many installations or “pods”. Here’s a list of pods — I recommend the socializer.cc pod.
WordPress is a free and open source blogging system.
Use Encrypted Voice and SMS
Wire is an app that allows you send encrypted text messages.
These apps allow you make encrypted phone calls: Signal (iOS) by Open Whisper Systems, Redphone (Android) by Open Whisper Systems, Ostel (Android), Silent Circle (iOS and Android).
These apps allow you create disposable phone numbers: Hushed, Burner (see more information in my article).
Use Computers and Mobile Devices That Don’t Track You
Currently, your best choice for a private mobile device is one that runs Android which is technically open source. However, the Android operating system provided with phones and tablets is often modified with the addition of proprietary applications from Google or others and may compromise your privacy.
The Blackphone is a privacy-friendly smart phone produced by Silent Circle. The phone features encrypted phone service, secure messaging and many other security-oriented features. See my article on Blackphone for more details.
You can also “jailbreak” an Android device, and replace the OS with Replicant (a free Android distribution) or CyanogenMod. See The Unlockr website for more information on how to unlock/root your device (or go directly to Cyanogenmod or F-Droid).
ThinkPenguin sells desktop and laptop computers that come with Linux pre-installed and pre-configured
Elementary OS is a Linux distribution that resembles Apple’s OS X. See my article for more details.
Secure Your Computers
Use a strong passwords for your user accounts.
Set your computer to log you out after 15 minutes.
Keep your systems and application updated, to avoid malware.
Encrypt your hard drives where possible. Some Mac and Linux installations have drive encryption built into the operating system — you just have to turn it on.
Secure Your Home Network
When setting up a wireless network use WPA2 encryption, use MAC address identification, set you network to not announce itself.
Set up you your router’s firewall — only open necessary ports. PeerGuardian is a privacy-oriented firewall application
Use A Private Operating System If You Need To Be Anonymous
Tails is a free operating-system designed to be used from a DVD or a USB stick independently of the computer’s original operating system. Tails can be run in “read-only” installation, meaning it does not write any files to disk. This provides a high level of privacy because the operating system leave no traces of the user’s activities, and there’s little chance of the user being monitored by key-loggers and other tracking software.
You can also run an OS inside a Virtual VM — see my article Running A Virtual Machine for more details.
More Recommendations
The Prism Break website is another good list of privacy-friend apps and service. These sites also have good recommendations: AlternativeTo, Quora and Reddit Open Source






Just want to thank you for the excellent and important work you do. You provide a much-needed (more and more critically needed each moment, in fact) service to everyone, and I commend you, and again, I thank you profusely. Peace.
I was wondering why you recommend startpage over duck as a search engine?
It’s because Startpage utilizes Google results (privately) — Google still has the most comprehensive search results.
Hi,
FYI: Disconnect does NOT hide your IP as it states. I thought it looked great but then my IP is still clearly found when I use it. The app does not hide your IP either.
I love your site here. Great information!
Ron
Thanks for the feedback.
Where does Disconnect claim to hide your IP address? This is what they state in their FAQ:
Their is a lot of disconnect.me services.
They provide :
Anti-trackers
Anti-Google-trackers
Anti-Facebook-trackers
Anti-Twitter-trackers
Proxy
Search engine
I believe (I don’t want to laught at you Ron) that Ron look at the proxy’s description and installed an anti-tracker. So his IP is clearly visible.
Personnaly I really like your website. A lot of data interesting. I’m doing like the same with some friends, but in french, stored here : http://sinformer.wikia.com/wiki/Comment_%C3%AAtre_anonyme_sur_internet
(Maybe one day I will translate)
And I just found a way to use bittorrent protocol using a free VPN : http://hide.me
It looks like to be the only one VPN that freely accepts to run bittorrent.
Thanks again, your job is really great. And I hope my advise for torrent will helps some.